In this blog series, our Executive Director Ben Taylor highlights a selection of cybersecurity, physical security, health or natural threat related stories from the past week.
Cybersecurity
Single Compromised Password Brought Down Colonial Pipeline
According to a cybersecurity consultant who worked on the Colonial Pipeline breach, the attack was the result of a single compromised password that was found on the dark web. The account that was utilized to access the system was no longer active at the time of the attack but allowed the threat actors to gain access through a VPN. The VPN account was also found to not be using multifactor authentication, allowing the attackers to gain access with just a username and password combo. It has not yet been determined if the group obtained the matching username, or were able to successfully guess it. If you have not established password protocols for your business, or feel they may need to be fine-tuned, this blog from Auth0 could be useful.
Physical Security
Scammers Continue Harassing Cannabis Businesses
Cannabis businesses are still experiencing high-level scammers, according to the Colorado Marijuana Enforcement Division(MED), which recently sent another warning to the state’s industry businesses about “intensifying instances” of fraud. The June 7 memo alerted cannabis business owners that con artists haven’t disappeared, despite multiple warnings from the MED. This is the fourth memo the MED has sent the industry since last October, with 48 fraud attempts (20% successful) reported across the state during that span. “Suspects successfully deceived employees into delivering cash or providing prepaid purchase card numbers, defrauding businesses of tens of thousands of dollars,” the MED memo notes. As the memo advises “All licensed employees must be vigilant to prevent these fraudulent attempts from becoming successful. Educating employees and preparing additional security measures is paramount. Business owners should create a protocol for the legitimate transfer of funds. Additional security measures may include creating a code word to authenticate valid requests for cash transactions from owners or managers.”
Natural Threats
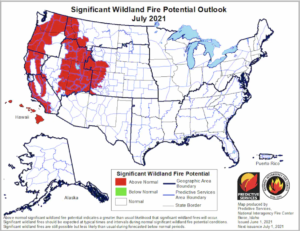
Intensifying California Drought Promises ‘Very Concerning’ Fire Season
California is entering its summer fire season with a high level of flammability. The hottest and most fire-prone months of the year are ahead. Conditions in the state are a striking example of escalating fire potential in the drought-stricken West. Crystal Kolden, a fire scientist at the University of California at Merced, said that what really stands out about this year’s fire season is how dry conditions are at higher elevations this early in the summer. The Sierra Nevada region is in the midst of one of its driest water years on record and saw rapid loss of critical snowpack this spring. Statewide snowpack officially hit 0 percent May 27. This was followed by an intense early-season heat wave as June got started. Last week in our Library Card Series we blogged about Ready.gov’s Wildfire Safety Guide, and recommend all organizations within areas of risk from wildfire check it out.
Security Podcast Updates
Gate 15 Risk Roundtable Podcast
Our friends at Gate 15 have released another round of their Risk Roundtable podcast where the crew jumps into summer with a new episode focused on some of the latest security news. Kicking off the episode, Dave and the team looks at the latest FBI report on Active Shooters (Active Shooter Incidents 20-Year Review, 2000-2019) and how organizations can integrate this information into their security planning and preparedness. Then they switch over to talk about a threat that grows stronger each month – Ransomware.
Be sure to check back every Tuesday as we publish our Library Card Series where we highlight one of the resources available in our library!
Check out the latest blog!
Tweet
