In this blog series, our Executive Director Ben Taylor highlights a selection of cybersecurity, physical security, health or natural threat related stories relevant to the cannabis industry.
Physical Security
Terrorgram Publishes ‘The Hard Reset’- To Inspire Future Hostile Attacks
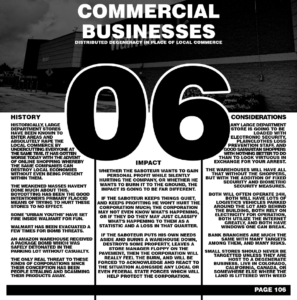
Yesterday, anti-government and White, Racially or Ethnically Motivated Violent Extremists (WRMVEs) Terrorgram published a 261 page propaganda document titled “The Hard Reset” which is filled with plenty of racist and antisemitic sentiments and discusses tactics, techniques, and procedures (TTP) and target selection for a wide variety of targets, to include politicians, and critical infrastructure, including Commercial Facilities, transportation, mass gatherings and more. Cannabis ISAO is working on an in-depth analysis of the wide-ranging document with several other information sharing partners, but there is an initial take-away for the cannabis industry.
In a section of the document which encourages attacks against large commercial businesses, the following statement is include, “Small stores should never be targeted unless they are host to a degenerate business live (SIC) in Colorado, California, Canada, or somewhere else where the land is littered with weed.” (see screenshot below) In addition, there is an entire page dedicated to discouraging followers from using cannabis which is littered with racial-charged language which we are choosing not to share.
While Cannabis ISAO considers this document representative of a very real ideology which exists in the world, and is becoming more and more vocal, we aren’t sharing it to sound alarmist. The facts are that extremists are operationalizing by themselves, online more and more, and propaganda such as this doesn’t need to spark a revolution, but inspire just one individual who has the ability to carry out devastating acts of terror. Often times documents such as these are cited by terrorists in their own writings prior to committing their hostile attacks, so we never take them lightly. And while the cannabis industry is not listed liberally throughout the document as some other industries, its mention is worth noting and is being shared for situational awareness.
As far as action items, as always it is important to remind employees, particularly in retail locations to remain vigilant and report suspicious activity. It is also beneficial to monitor local protest and rally activity to identify times where security postures may need to be raised. For instance, if a white nationalist group is holding an event in a city where your organization has a retail establishment, it may be worth considering employing additional security guards around that time. Those type of groups will be very familiar with this publication, and added security can help reduce chances of a “target of opportunity” type of incident.
Sacramento City Officials Offering Cannabis Businesses Up to $4K to Upgrade Security
The City of Sacramento is offering cannabis businesses up to $4,000 to purchase new or upgraded security systems. According to the City of Sacramento, starting July 7, cannabis businesses could begin applying for the rebate from the Office of Cannabis Management. Businesses are able to use this rebate to purchase new or upgraded security systems to comply with the city’s new cannabis security requirements.
“Thank you to the Department of Cannabis Control for making these funds available so local cannabis businesses can more easily meet local and state security compliance,” said City Cannabis Manager Davina Smith. “These rebates will help keep our local cannabis businesses safe and will support the City’s equity program by supporting a quicker path to obtaining local permits and annual state licensing.”
More information on the rebate program requirements, eligibility, and submittal forms can be found on the Office of Cannabis Management’s website.
Cybersecurity
Cyber Safety Review Board Releases Unprecedented Report of its Review into Log4J Vulnerabilities and Response
Earlier this week, the U.S. Department of Homeland Security (DHS) released the Cyber Safety Review Board’s (CSRB) first report, which includes 19 actionable recommendations for government and industry. The recommendations from the CSRB – an unprecedented public-private initiative that brings together government and industry leaders to review and assess significant cybersecurity events to better protect our nation’s networks and infrastructure – address the continued risk posed by vulnerabilities discovered in late 2021 in the widely used Log4j open-source software library. These are among the most serious vulnerabilities discovered in recent years. The CSRB’s recommendations focus on driving better security in software products and enhancing public and private sector organizations’ ability to respond to severe vulnerabilities. This report was delivered to President Biden through Secretary of Homeland Security Alejandro N. Mayorkas.
“At this critical juncture in our nation’s cybersecurity, when our ability to handle risk is not keeping pace with advances in the digital space, the Cyber Safety Review Board is a new and transformational institution that will advance our cyber resilience in unprecedented ways,” said Secretary Mayorkas. “The CSRB’s first-of-its-kind review has provided us – government and industry alike – with clear, actionable recommendations that DHS will help implement to strengthen our cyber resilience and advance the public-private partnership that is so vital to our collective security.”
The CSRB conducted its review in the public interest and recommended the release of its full report to the public. In keeping with his commitment to improving transparency, Secretary Mayorkas followed that recommendation to enable both public and private partners to fully benefit from the CSRB’s review.
The CSRB is composed of highly esteemed cybersecurity leaders from the federal government and the private sector. The CSRB does not have regulatory powers and is not an enforcement authority. Instead, its purpose is to identify and share lessons learned to enable advances in national cybersecurity. Robert Silvers, DHS Under Secretary for Policy, serves as Chair and Heather Adkins, Google’s Vice President for Security Engineering, serves as Deputy Chair.
How a Fake Job Offer Took Down the World’s Most Popular Crypto Game
Ronin, the Ethereum-linked sidechain that underpins play-to-earn game Axie Infinity, lost $540 million in crypto to an exploit in March. While the U.S. government later tied the incident to North Korean hacking group Lazarus, full details of how the exploit was carried out have not been disclosed. According to two people with direct knowledge of the matter, who were granted anonymity due to the sensitive nature of the incident, a senior engineer at Axie Infinity was duped into applying for a job at a company that, in reality, did not exist. After what one source described as multiple rounds of interviews, a Sky Mavis engineer was offered a job with an extremely generous compensation package. The fake “offer” was delivered in the form of a PDF document, which the engineer downloaded — allowing spyware to infiltrate Ronin’s systems. From there, hackers were able to attack and take over four out of nine validators on the Ronin network — leaving them just one validator short of total control. The incident demonstrates that an insider threat does not need to be malicious in order to cause a costly security incident to an organization.
New Scam Targeting Restaurants Could Be Used Against Cannabis Retail
In a new scam targeting restaurants, criminals are leaving negative ratings on restaurants’ Google pages as a bargaining chip to extort digital gift cards. Restaurateurs from San Francisco to New York, many from establishments with Michelin stars, said in recent days that they’ve received a blitz of one-star ratings on Google, with no description or photos, from people they said have never eaten at their restaurants. Soon after the reviews, many owners said, they received emails from a person claiming responsibility and requesting a $75 Google Play gift card to remove the ratings. If payment is not received, the message says, more bad ratings will follow. While current reporting suggests that restaurants are being targeted, any business that relies on online review could see themselves targeted in similar fashion, particularly if the scam continues to be effective against restaurants.
The text threat was the same in each email: “We sincerely apologize for our actions, and would not want to harm your business but we have no other choice.” The email went on to say that the sender lives in India and that the resale value of the gift card could provide several weeks of income for the sender’s family. The emails, from several Gmail accounts, requested payment to a Proton mail account.
Law enforcement officials have urged restaurant owners to contact Google if they’ve been targeted, and to report these crimes to their local police departments, as well as the F.B.I. and the Federal Trade Commission. The commission advises businesses not to pay the scammers.
Small and Midsize Businesses Being Targeted with Ransomware
A group of actors originating from North Korea that the Microsoft Threat Intelligence Center (MSTIC) tracks as DEV-0530 have been developing and using ransomware in attacks since June 2021. This group, which calls itself H0lyGh0st, utilizes a ransomware payload with the same name for its campaigns and has successfully compromised small businesses in multiple countries as early as September 2021. Microsoft encourages all organizations to proactively implement and frequently validate a data backup and restore plan as part of broader protection against ransomware and extortion threats.
Multifactor authentication, in which a login attempt is verified by additional layers of protection such as the use of codes sent by text messages, phone calls or dedicated apps, is a relatively simple defense against hackers.
Yet a survey of around 1,400 small and medium businesses globally conducted by the U.S.-based nonprofit Cyber Readiness Institute, and published Tuesday, finds that 55% of companies haven’t set up multifactor authentication. Of those that have, only 28% require employees to use it.
A recent post in NY Cannabis Insider discusses how cannabis businesses can’t afford to ignore cybersecurity.
Check out the latest blog highlighting issues important to cannabis security!
Tweet
